Sitecore 10 Authenticated File upload to RCE / CVE-2021-38366
After looking for some extreme hardening of the Sitecore client I found a way to get Remote Code execution (RCE) via a Update center, described in this post.
It is possible for authenticated users, to upload arbitrary files, via update package functionality.It is possible for a malicious attacker to bypass file upload restrictions, hardened with the Sitecore hardening guide https://doc.sitecore.com/en/developers/101/platform-administration-and-architecture/security-guide.html and with secure file upload functionality, taken from this link
https://doc.sitecore.com/developers/100/platform-administration-and-architecture/en/secure-thefile-upload-functionality.html.
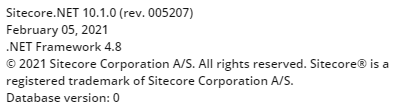
Test Instance information
The test of this was done on a local Windows 10 machine with Sitecore 10 XM installation, installed via Graphical installation wizard see more information below
The Additional Filed upload restriction package was also installed with the following settings.
<?xml version="1.0" encoding="utf-8"?>
<configuration xmlns:patch="http://www.sitecore.net/xmlconfig/">
<sitecore>
<processors>
<uiUpload>
<processor mode="on"
type="Sitecore.Pipelines.Upload.CheckExtension,
Sitecore.UploadFilter" patch:before="*[1]">
<param desc="Allowed extensions (comma separated)"></param>
<param desc="Blocked extensions (comma separated)">exe,dll,aspx</param>
</processor>
</uiUpload>
</processors>
</sitecore>
</configuration>Steps to reproduce
Keep in mind this is a autheticated file upload, so a compromised user must be obtained.
- Authenticate / Login to Sitecore
2. Once correctly logged in. Navigate to the Upload center
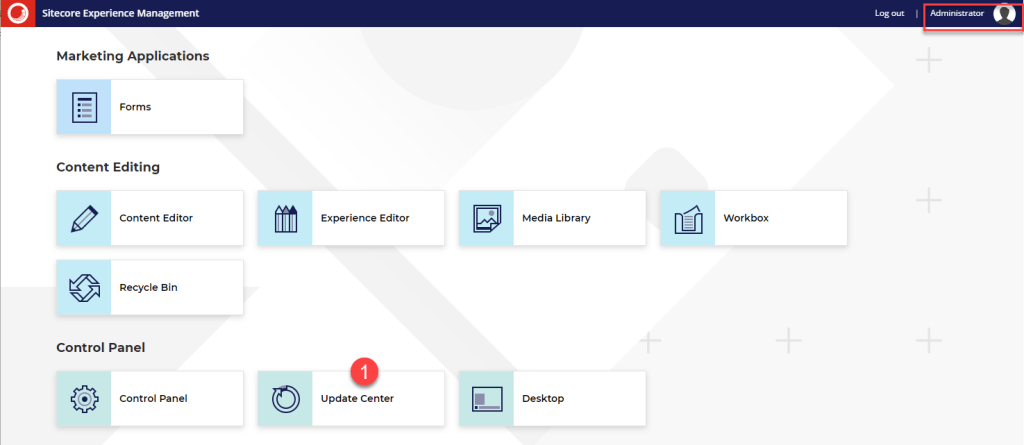
3. Choose/click the option to upload custom update

4. Pick your custom webshell

5. If the installer hangs click anywhere in the windows, this is expected.

6. Since uploads of updates packages always goes into the same folder
https://HOSTNAME/sitecore/admin/Packages/
to find the uploaded file in our case
https://sc101cm.dev.local/sitecore/admin/Packages/shell.aspx
7. Now all that is left is running the webshell.
Remediation
Disabled the Update center functionality
One way of doing the in add restriction to path in web.config like below
<location path="sitecore/api/ssc/updatecenter">
<system.web>
<authorization>
<deny users="*" />
</authorization>
</system.web>
</location>Other
The findings has been reported to Sitecore, and the Update center is being deprecated, but until this happens a simple fix is as mentioned to disabled the Update center functionality.
This vulnerability has been given CVE-2021-38366










You say the remediation is to disable the update center. How do you go about doing this?
Hi Kenneth
Sorry somehow this part was missing, I’ve added in again, there might be better ways to do it but then one shown will limit all access to the updatecenter